Your Roadmap from Spreadsheet Chaos to Compliance
Go from disorganized IT chaos to a trusted, organized state. Demonstrate security readiness to clients and auditors — without being an expert.
Go from disorganized IT chaos to a trusted, organized state. Demonstrate security readiness to clients and auditors — without being an expert.
We guide you step-by-step from scattered documentation to organized, audit-ready IT operations. No expertise required.
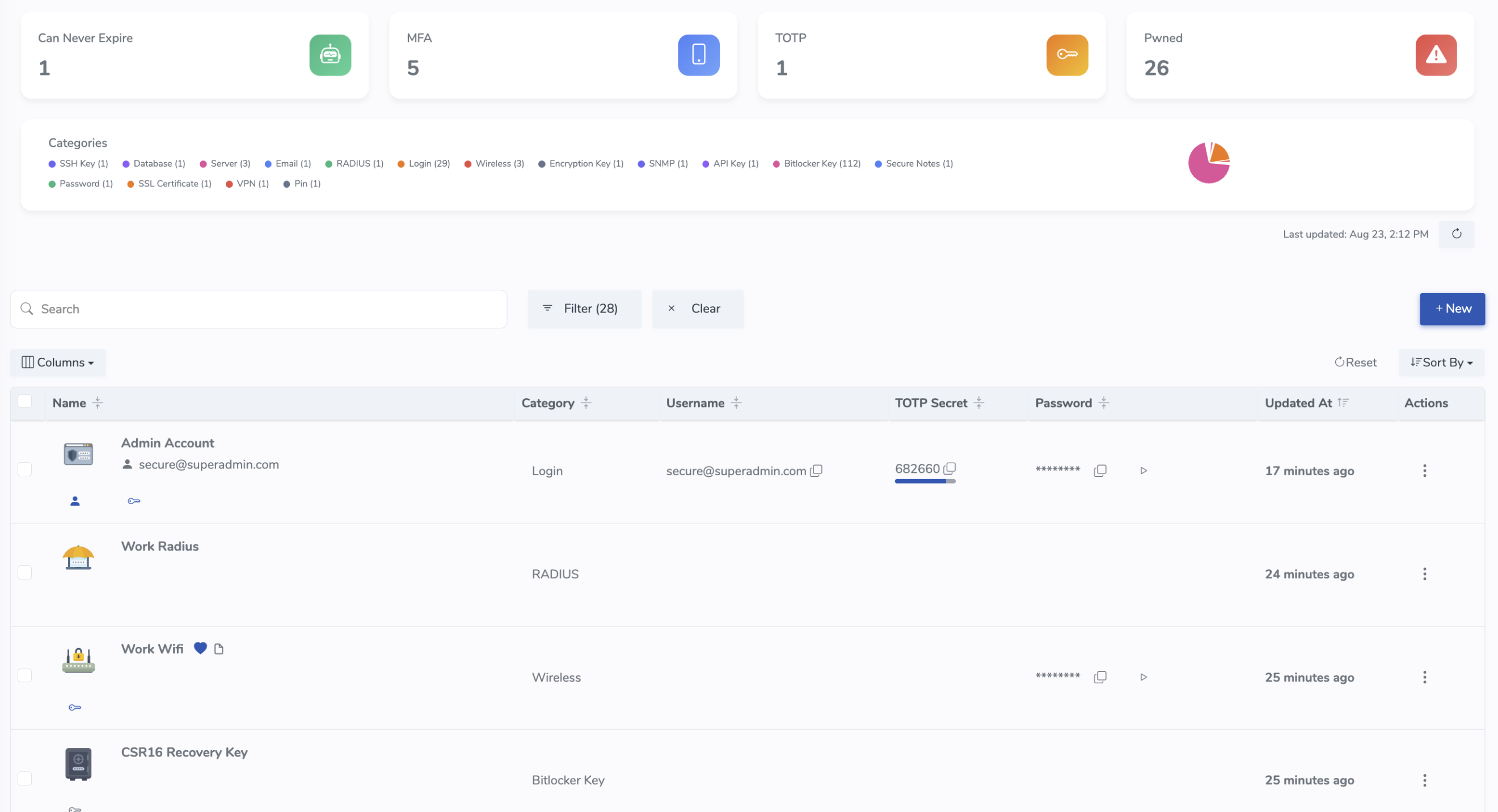
Track devices, networks, VMs, racks/shelves & IPs. Auto-pull Dell/Lenovo/HP warranties; monitor SSL certificates; scan open ports.
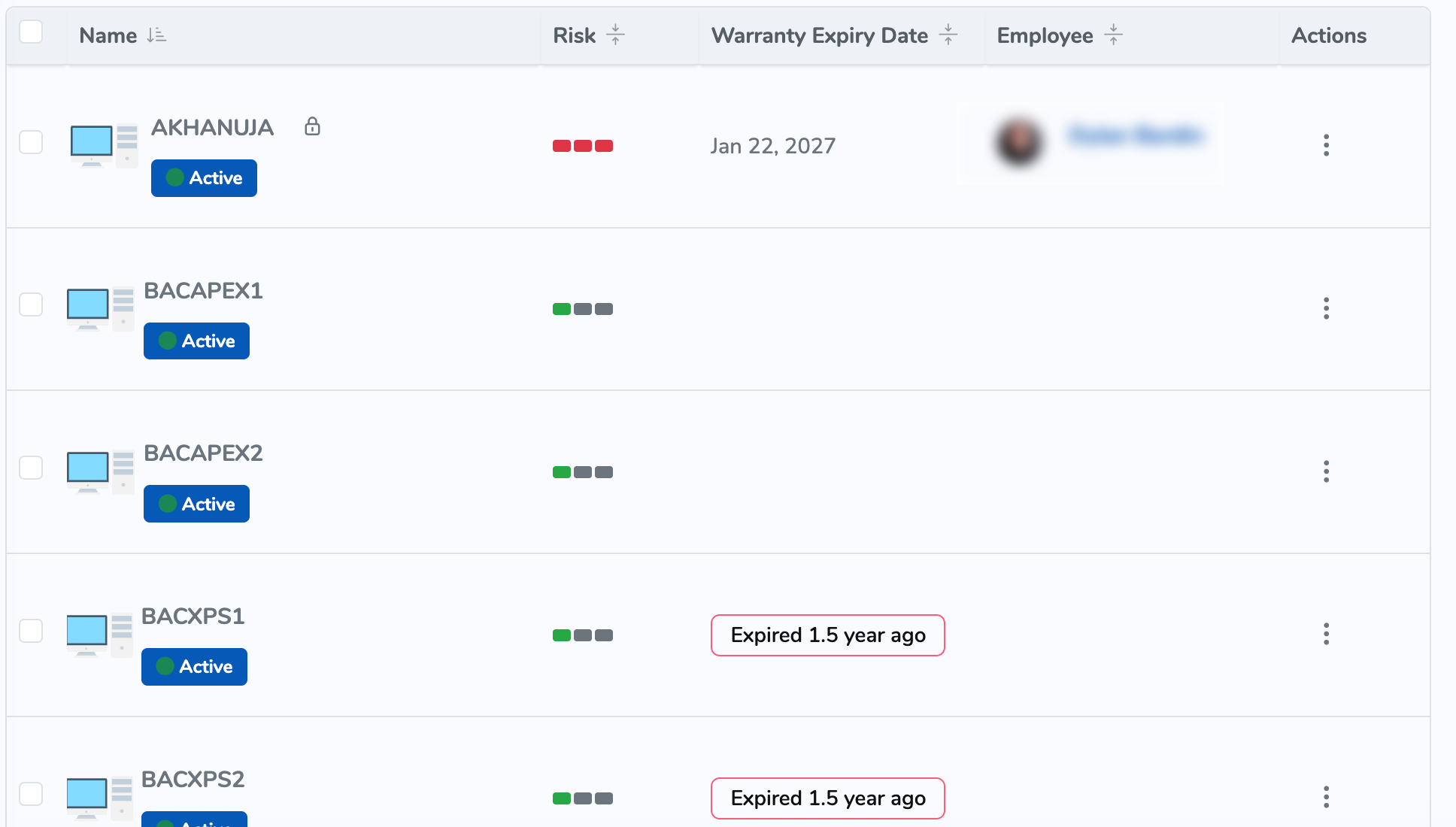
Built-in SPF, DKIM & DMARC verification to reduce spoofing and deliverability issues.
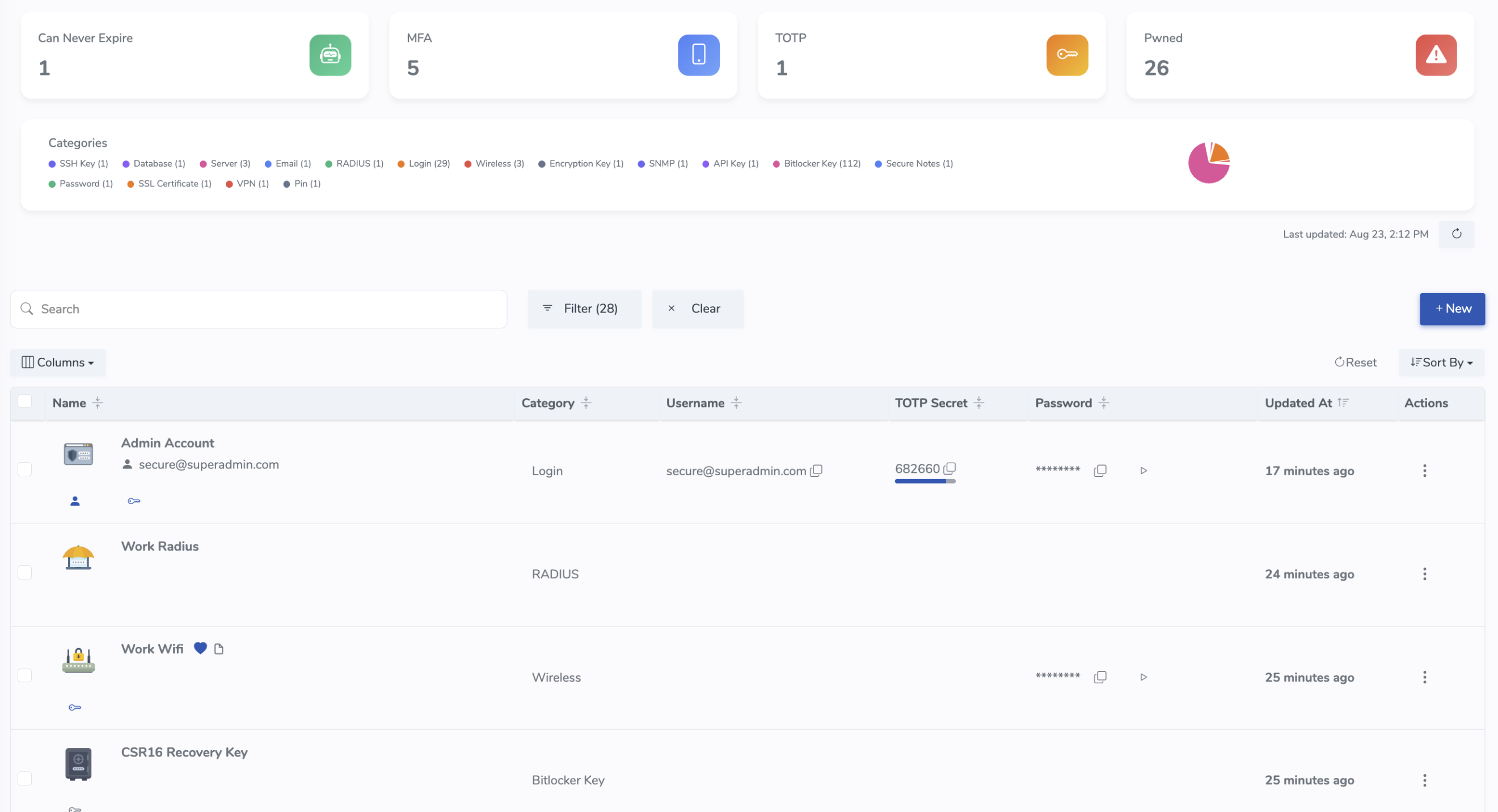
Store credentials securely with two-factor codes, track access, and get alerted when passwords are breached.
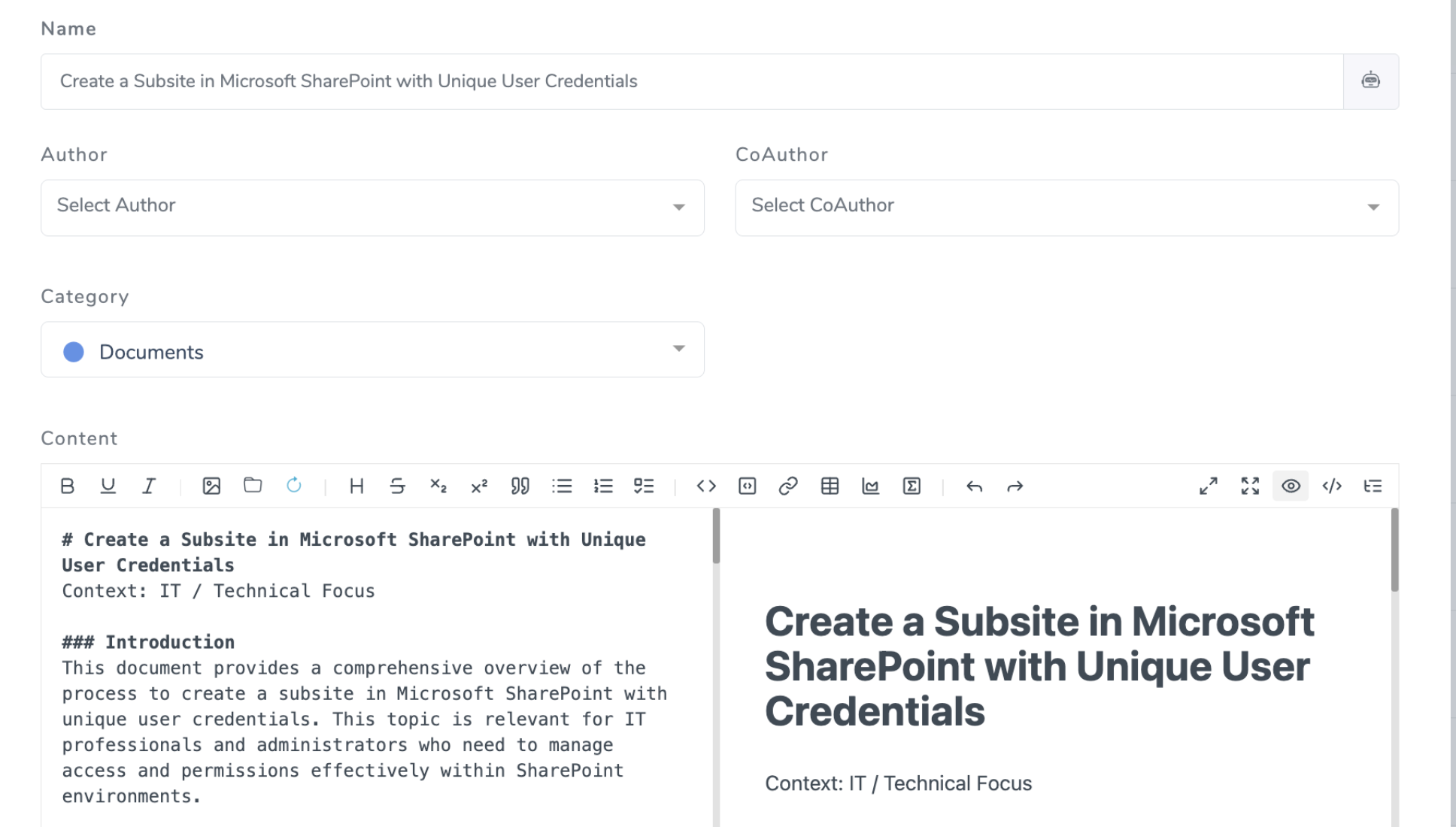
Mermaid diagrams, rack views, and Markdown+ docs with smart @-references to any asset or record.
Reduce time-to-resolve by centralizing knowledge, credentials, diagrams, and workflows in one system.
Passwords scattered in multiple locations, network diagrams buried in email threads, vendor contracts lost in various systems
Hours wasted searching for server credentials while your business operations grind to a halt
Critical information locked in employees' heads, vanishing when team members leave the company
Surprise renewals and forgotten subscriptions bleeding your budget dry
The productivity killer: IT teams waste 30% of their time hunting for information instead of solving problems and driving innovation.
Run and protect your IT foundation.
Monitor devices, networks, VMs, and cloud storage with compliance status, risk scores, and auto warranty checks for Dell, Lenovo, and HP computers.
Diagram networks, use Mermaid diagrams, manage racks & shelves, monitor SSL Certificates, verify SPF/DMARC/DKIM, and scan open ports for proactive security.
Securely store passwords & secrets with two-factor codes and dark web monitoring. Know when credentials are viewed and when passwords are compromised.
Capture knowledge. Standardize processes. Work smarter.
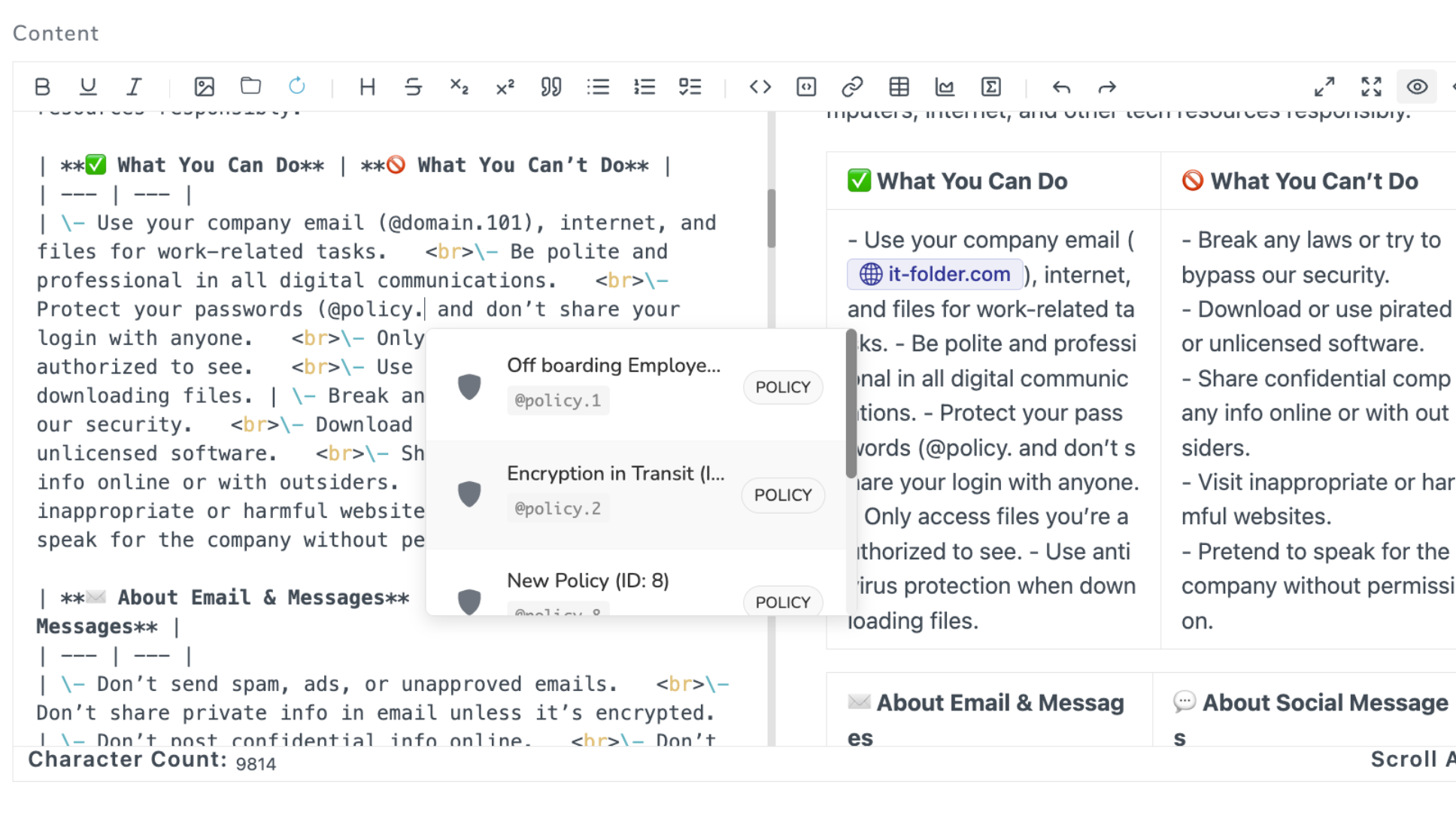
Turn tribal knowledge into a searchable KB with @-tag linking for all your IT assets and documents.
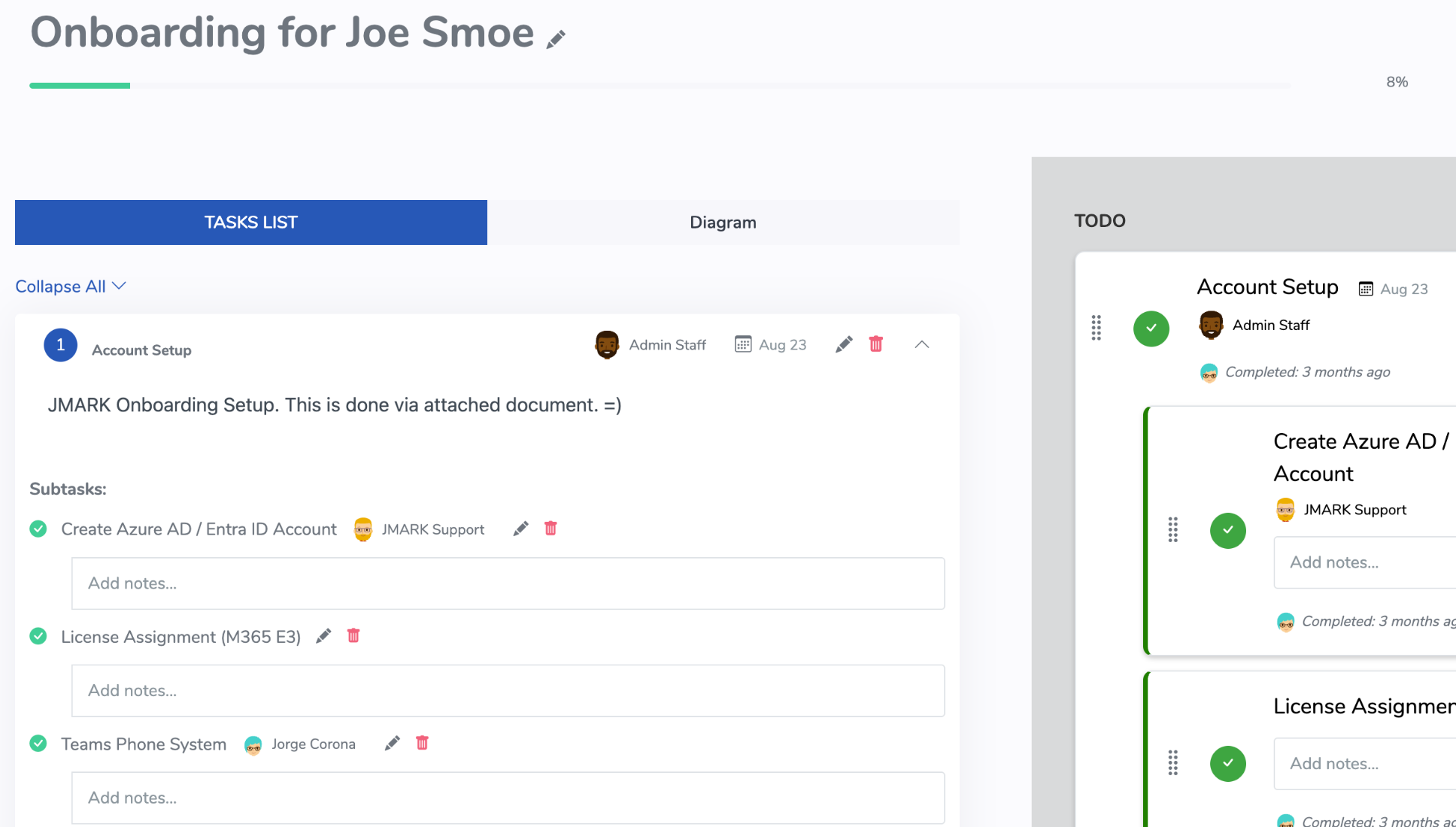
Standardize onboarding/offboarding and recurring workflows with task assignment and progress tracking.
Find any device, document, or credential instantly with natural-language AI search. Local models by default, or connect OpenAI for enhanced capabilities.
Stay compliant, manage change, and master your IT spend.
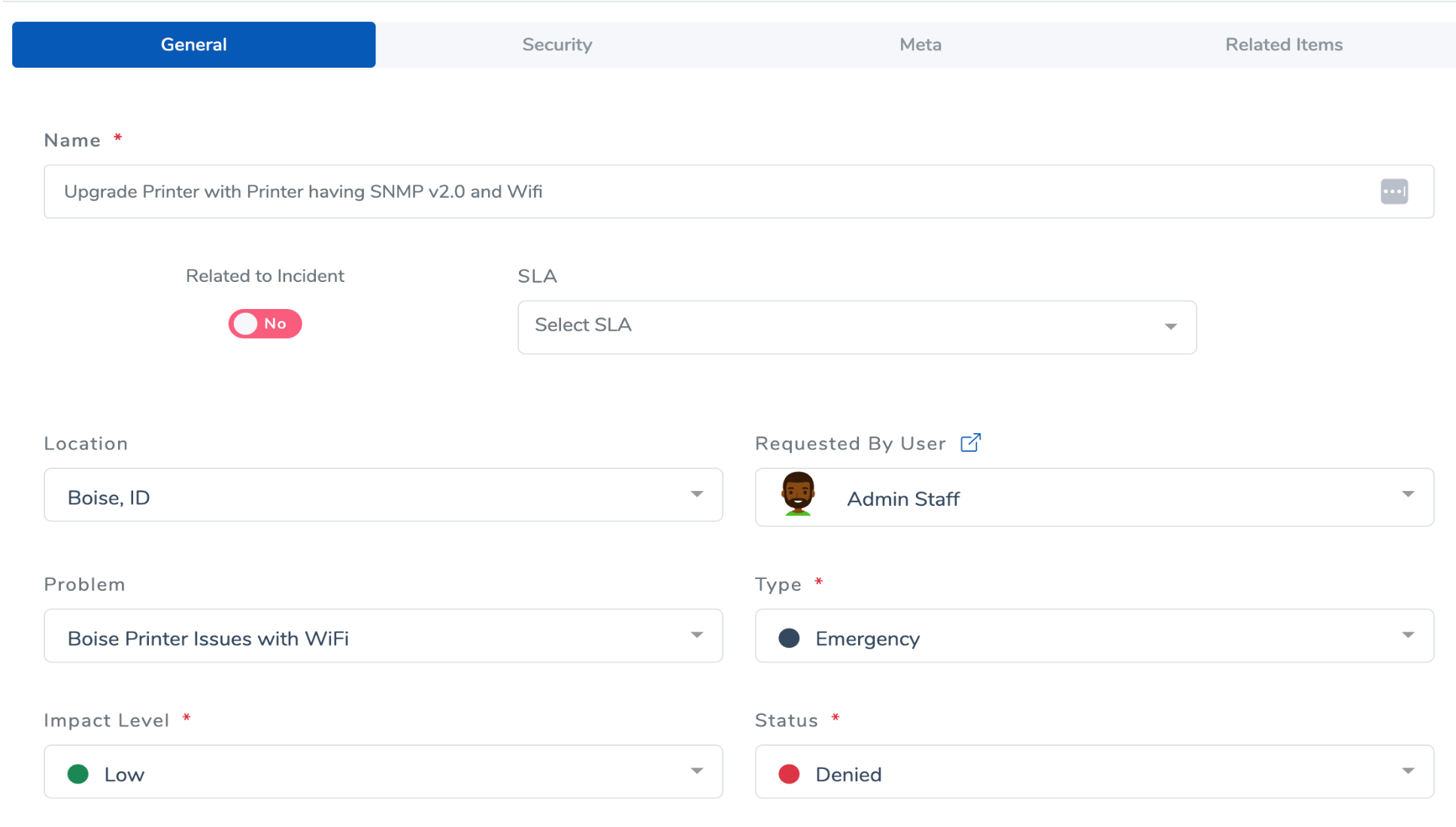
Streamlined ITSM with issue logging, problem tracking, change request workflows, configurable SLAs, and seamless Zendesk ticket integration.

Create Policies and Controls, Contracts, and risk assessments. Generate reports and monitor risk heatmaps with continuous compliance checks.
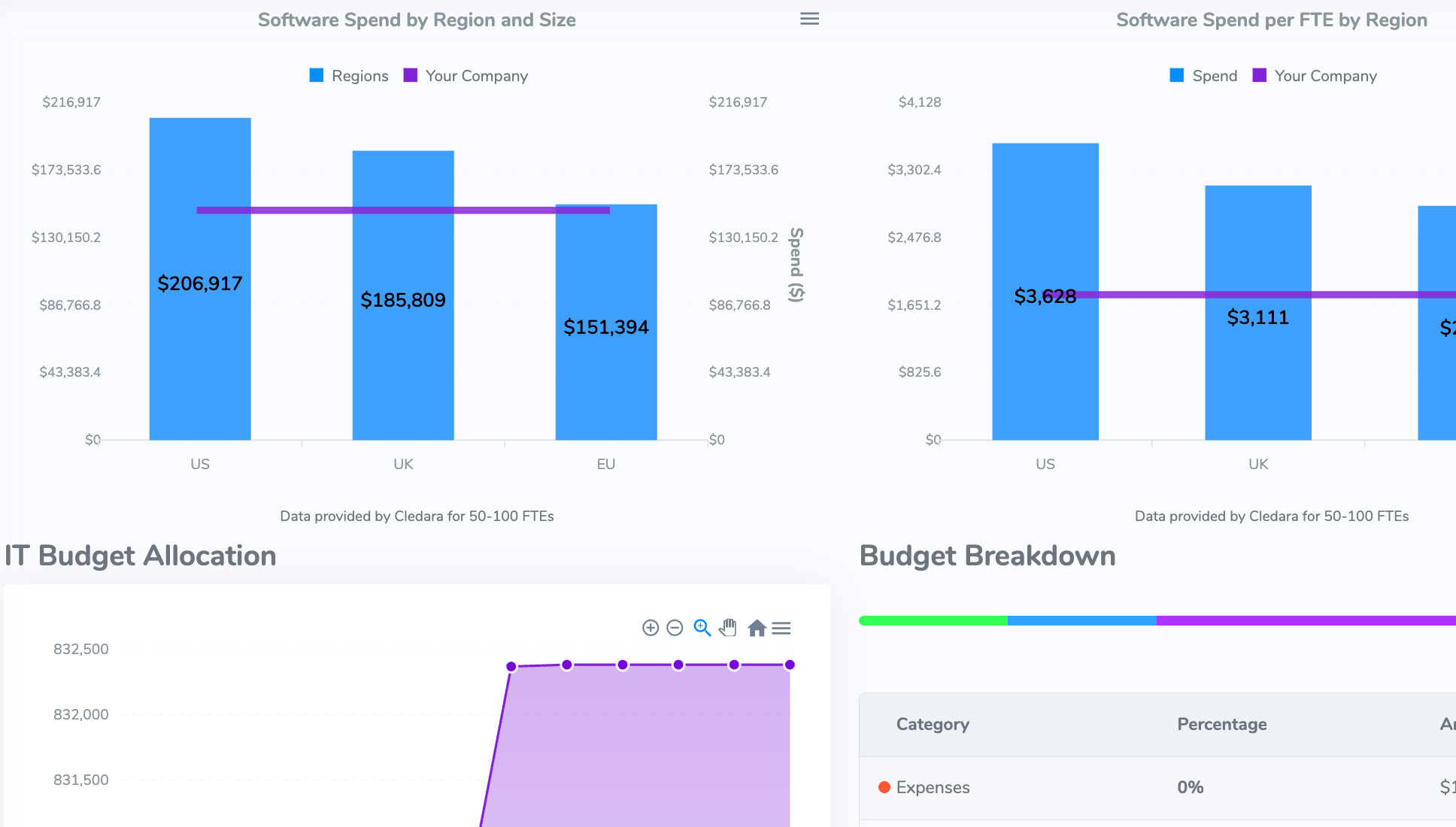
Track subscriptions, services, expenses, projects, compensations, and create budgets that have comparisons to industry spending.
Connect IT Folder with your existing tech stack for a unified, streamlined workflow that works with your current tools.
Your sensitive IT data deserves the highest level of protection. We've built security into every layer.
Military-grade encryption for all sensitive data at rest.
Each sensitive field gets its own encryption key, automatically managed and rotated.
Secure every login with time-based one-time passwords via authenticator apps.
Every account gets dedicated, encrypted storage for documents and files.
Everything included. One easy price.
Addressing your concerns about security, data management, and platform functionality.
all-MiniLM-L6-v2 for
fast, local embedding and search. You can also provide your OpenAI API key to use text-embedding-ada-002.
Note: with OpenAI, data is sent externally and OpenAI usage charges apply.
Stop wasting 30% of your time hunting for information. Get started in minutes with our 14-day free trial.